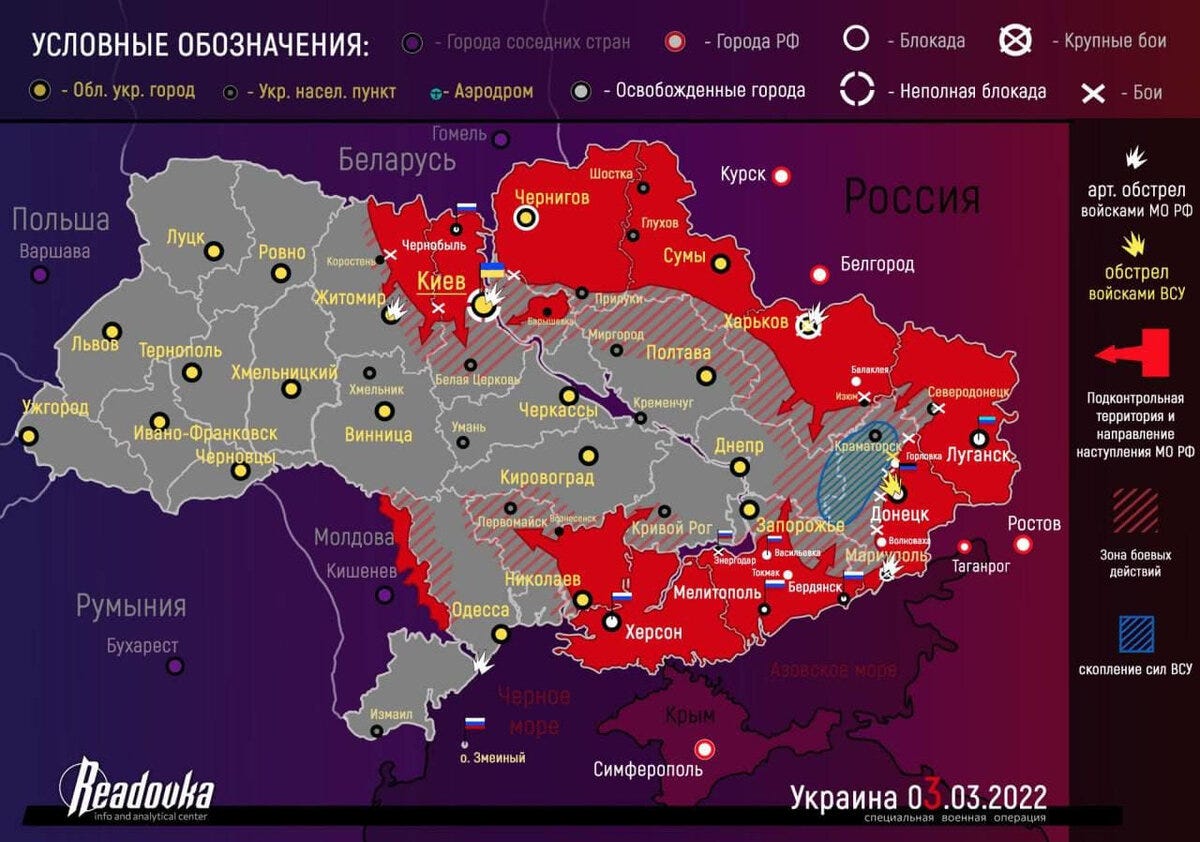
There are two Ukraine wars currently. One's on the ground, one's in the air (the information war).
The information war's been a rout up to now. The war on the ground is going irrevocably in precisely the opposite direction. Although the talking heads will squirm and scrap about it, the outcome of the war in the air is also given.
“Zensursula” is trying to shut down parts of the Internets in the EU. People in North America have slim pickings. For those having trouble reaching RU sites, here's some general info.
YOUR PRIVACY
Most of you signing up for the SP Substack already know, so what follows is preaching to the choir, so we'll keep it brief. We're assuming most of you use throwaway addresses when signing up for stuff, but to make sure: read up on PRISM if you need to.
https://infogalactic.com/info/PRISM_(surveillance_program)
PRISM was revealed by Edward Snowden. James Clapper lied before the US Congress when denying this was going on. It was Clapper's lies - he hides his face as he does it - that pushed Snowden over the edge and got him to break for Hong Kong.
Those known to be part of PRISM are: Microsoft, Yahoo, Google, Facebook, Paltalk, YouTube, AOL, Skype, and Apple. Your data is not secure with any of those companies. Those are the companies known of and not necessarily the only ones. Stories that PRISM's been shut down cannot be trusted, any more than stories that Operation Mockingbird has been shut down can be trusted. (Operation Mockingbird is doing fine, thank you - just look at the media landscape in the West today.)
Google is known to be overly ambitious, but there's no guarantee that the other companies haven't caught up, or that they all haven't gone even further today. ISP companies use DHCP less and less, if at all. Subscribers get static IPs. Web browsers gleefully offer up lots of identifying information, including device MAC numbers. PRISM companies can easily build personal profiles on you at very little cost, and the data can lead back to you personally. Several companies are known to implement web-based keystroke loggers, so the old trick used by the people planning 9/11 will no longer work. Data storage is reliable and cheap, and the dividends on archiving this data are enormous. So use secure mail for sensitive things.
Secure Correspondence
Belgium used to be good. The alphabet agencies tried to break into Belgium, reportedly to no avail, yet the free services started shutting down.
Russian mail - mail.ru - might not be any better.
And there's always the "man in the middle" to think about. Using a hacked device is something to also think about.
Our opinion is that mobile devices are insecure, and anything emanating from Redmond is also insecure, not to speak of Google Android and Chrome, and Apple can turn out to the the worst of the lot.
Great news, wouldn't you agree?
Things You Can Do
The two things you can do for your own safety are 1) stop using insecure devices and 2) use only secure mail for important correspondence.
There are several sites that offer secure mail. RISEUP has servers in the US and is by invitation only. But they have what appears to be a free VPN, and we're testing it now. So far it works - mostly.
Riseup's VPN is based on this.
https://bitmask.net/en/install
Note that "old" is not always a bad thing anymore. And open source implementations are generically more trustworthy.
Tutanota is German-based secure webmail but has some funky gotchas.
ProtonMail is based in Switzerland and is very popular.
Here's the thing. Provided those you correspond with are on the same network, there's little chance your correspondence will ever reach the outside world.
A good secure system should keep your correspondence encrypted on its servers, so even the operators can't read it.
Sending mail outside the network will at least reveal the "metadata" - the from, the to, the subject line. That can be enough sometimes.
All the above was of course preaching to the choir for most of you, but now it's done and now we can move on to other things.
Reaching RU Sites
Google's blocking everything from Russian sites like RT. Russian sites are taking measures to protect against ongoing DDoS attacks.
RT.com, SPUTNIKNEWS.com, KREMLIN.ru: The first two are easy through VPN. Kremlin? You'd think. It takes time - a long time.
inetnum: 95.173.128.0 - 95.173.143.255netname: RSNETdescr: RUSSIAN STATE INTERNET NETWORKcountry: RUTor is less useable. YMMV.
RT.com reduced their hourly news updates. (Some presenters have resigned? We'll see tomorrow.)
RT documentaries are good, and contain a lot of info westerners know nothing about.
What's emerged is that western MSM seem to have suppressed the story of the Nazism in the Ukraine, this by simply dismissing the idea that Ukraine can hardly be Nazi when their president is Jewish.
That's the magic of it. That's precisely what's going on. That's what this is ultimately about. That's what Putin talked about in his 0600 speech 24 February - he wants to redo June 1940. The CIA gave him the chance.
This site is surprisingly available, and it's one of the sites consulted in the West:
https://readovka.news/news/feed
You can concentrate on the right margin called "Главное" - those are their major headlines.
We've checked their special on the history of the conflict in the Donbass, and it's very detailed and sticks to dates and facts (lots of dates and facts).
https://readovka.news/news/84513
There'll be more later from MoA and the Saker.
-SP